About

Hi, I’m Brian D'Hurieux., a network analyst and software developer with over 15 years of development experience and a strong focus on cybersecurity. I analyze network traffic, automate detection workflows, and build tools that make threat data easier to see and understand.
My background blends network forensics and full-stack development. I’ve worked on everything from packet capture analysis to building secure web applications that support large-scale awareness and defense efforts.







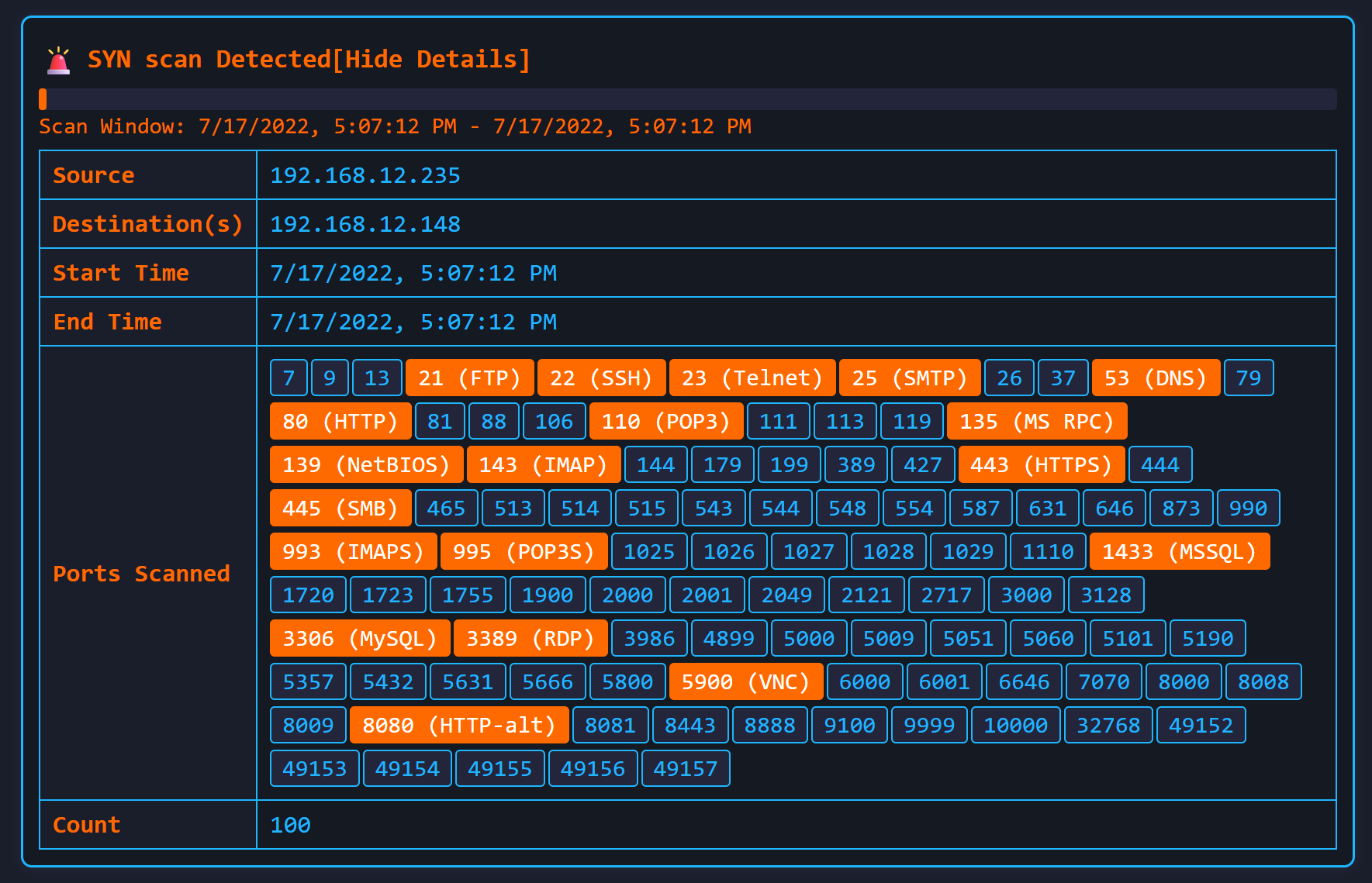
 FireShark
FireShark